Web Intelligence
for a Safer World
Empowering Safety and Security
Protecting Communities. Analyzing Threats. safeguarding Organizations.
Protecting Communities. Analyzing Threats. Safeguarding Organizations.

Law enforcement
Accelerate criminal investigations, enable emergency response, locate missing people, interdict human trafficking, and mitigate public safety threats.

government
Protect from nationwide threats, conduct intelligence investigations, make informed and data-driven decisions, and maintain situational awareness.

Financial Institutions
Conduct due diligence, investigate money laundering and fraud, support compliance efforts, and deliver insights on potential risks before they fully develop.

Corporations
Secure organizations, people and assets, identify data breaches, and perform digital and physical risk assessments to strengthen the security posture.
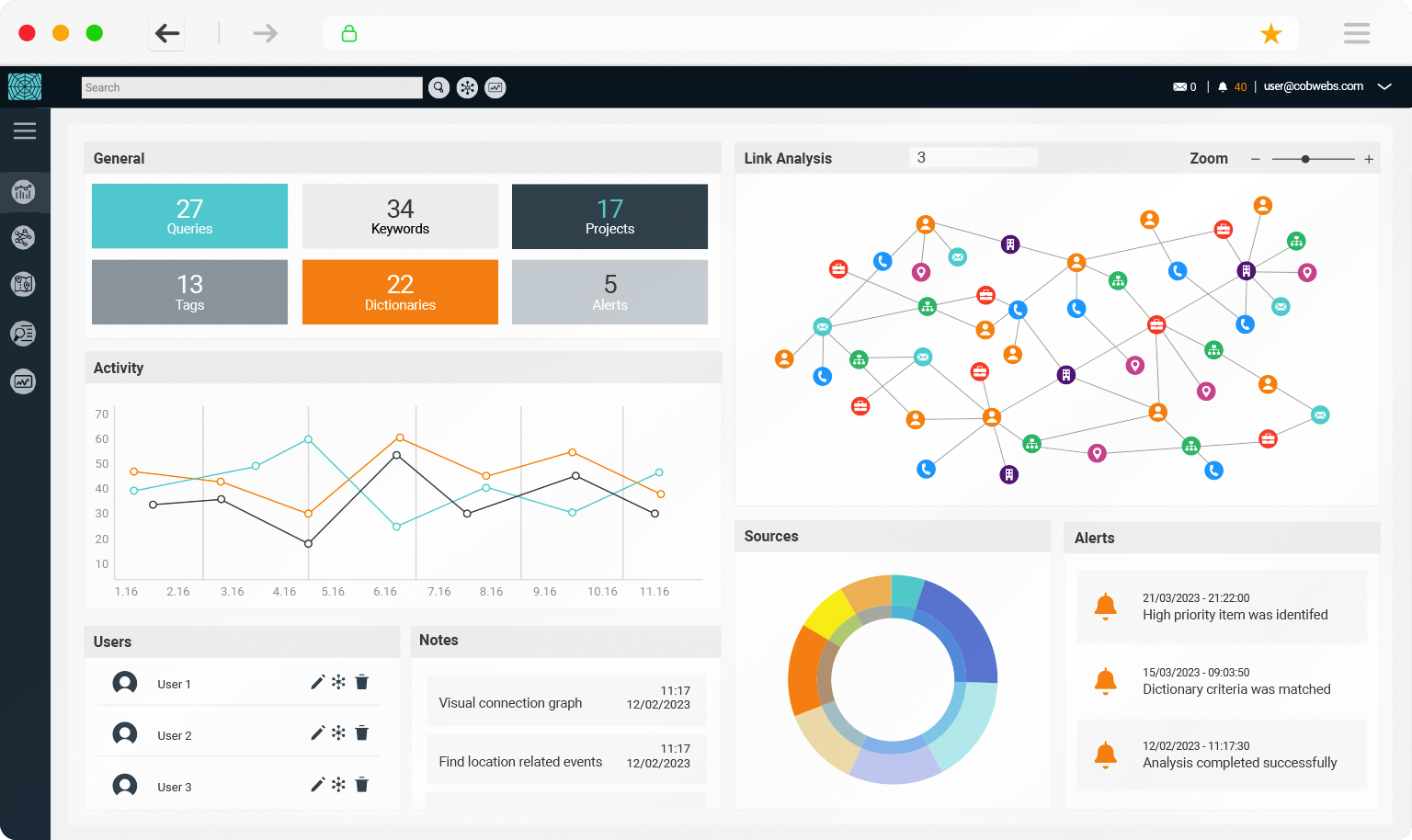
The Premier Solution in Open-Source Intelligence
Designed by intelligence and security experts, our solution enables seamless search and analysis of publicly available sources, open, deep and dark web, as well as integrated data sources, allowing you to generate actionable insights.
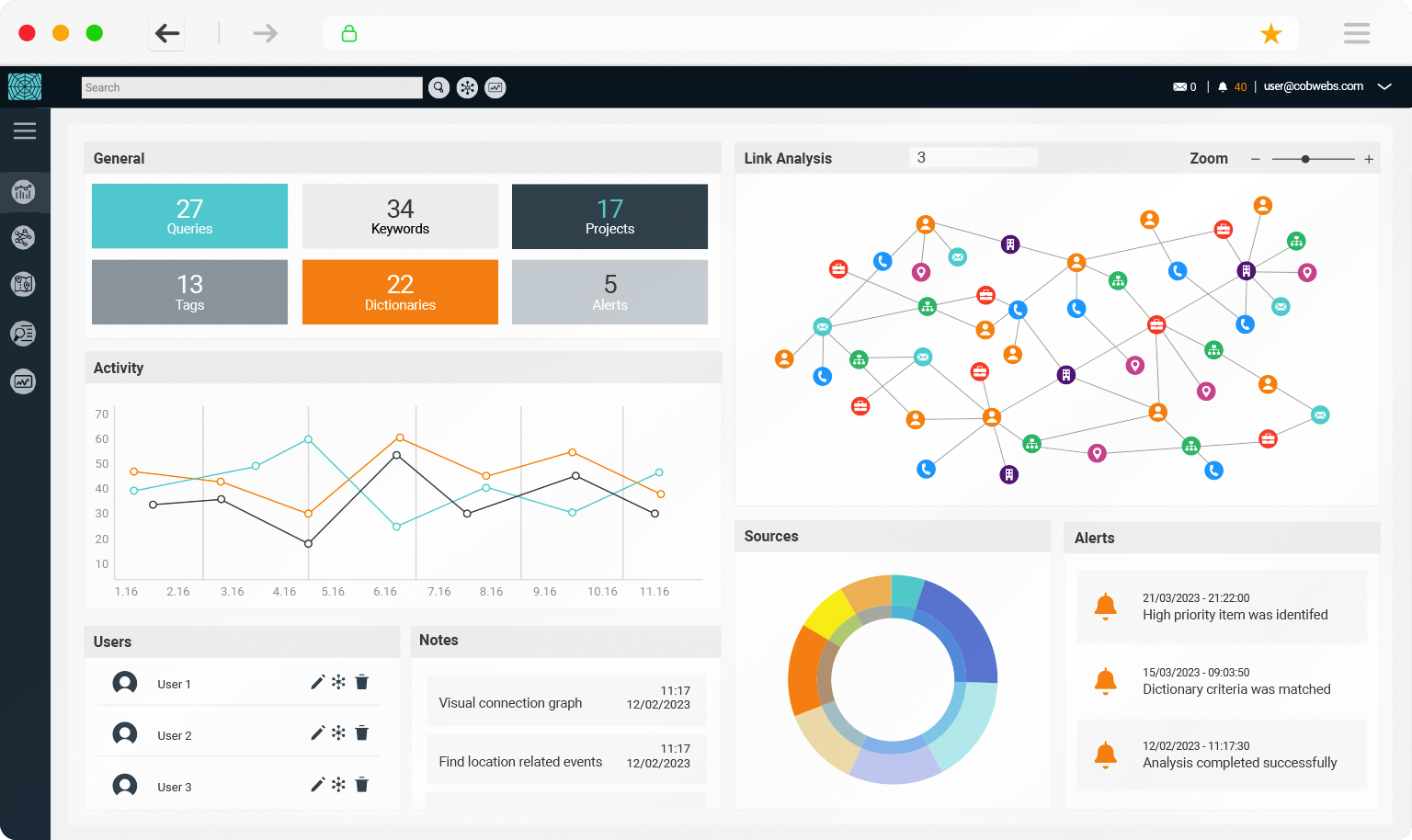
AI-Powered Investigations and Threat Monitoring
Streamlined with artificial intelligence tools, our Web Intelligence (WEBINT) platform enables users to search and analyze the web’s big data using the latest machine learning algorithms. Our solutions are an investigative force multiplier, delivering real-time insights, illuminating hidden leads and automatically connecting the dots.
Web Discovery
Covering Millions
of Sources
Streamlined AI
for Actionable
Insights
Reveal Hidden
Relationships to
Detect Patterns
Visual Link
Analysis to Connect
the Dots
Real-Time
Alerts to Detect
Threats
Dynamic Reports
to Streamline
Intelligence
Unleash the Power of Digital Intelligence
Comprehensive
Platform
Dynamic and scalable, providing seamless access to open, deep, and dark web. Generating real-time intelligence.
Automating
Manual Work
Automates manual workflows, and accelerate investigations to minutes
instead of weeks.
Winning
Technology
AI-Powered, award winning technology that solves complex real-world challenges and produces invaluable insights.
Operational
efficiency
Close more cases faster, detect threats as they occur, and share knowledge in a unified platform.
End-to-End
Solution
A multi-layered platform with extensive capabilities, adapted to digital investigations and threat monitoring.
Domain
knowledge expertise
Deep industry knowledge that provides customers with extensive training and resources.
I've been working this case for over 5 months and after adding Cobwebs to our investigative toolkit, this evidence was identified in under 5 minutes. Cobwebs platform has truly revolutionized the way we conduct our investigations."
Cyber Crime Analyst
Special Investigations Unit
Unleash the Power of Digital Intelligence
Comprehensive Platform
Dynamic and scalable, providing seamless
access to open, deep, and dark web.
Generating real-time intelligence.
Automating Manual Work
Automates manual workflows, and accelerate investigations to minutes instead of weeks.
Winning Technology
AI-Powered, award winning technology that solves complex real-world challenges and produces invaluable insights.
Operational efficiency
Close more cases faster, detect threats
as they occur, and share knowledge
in a unified platform.
End-to-End Solution
A multi-layered platform with extensive capabilities, adapted to digital investigations and threat monitoring.
Domain knowledge expertise
Deep industry knowledge that provides customers with extensive training and resources.
I've been working this case for over 5 months and after adding Cobwebs to our investigative toolkit, this evidence was identified in under 5 minutes.
Cobwebs platform has truly
revolutionized the way we
conduct our investigations.
-
Cyber Crime Analyst
Special Investigations Unit
Product Portfolio
Designed for Investigators and Analysts, and tailored for their operational requirements, providing an enhanced yet user-friendly solution.
Digital Investigations
Search, analyze, and extract critical, intelligent insights with ease and efficiency from millions of online sources and integrated data records
Threat Intelligence
Gauge the state of your digital and physical assets, and gain unmatched situational awareness with real-time intelligence insights
Financial Investigations
Accelerate financial investigations, AML, fraud and other illicit activities to enable safer, more efficient due diligence and risk analysis
Secured Analyst
Maintain secured and
compliant web
investigations, powered by AI tools, with a secured, isolated workflow environment
Why Cobwebs Technologies
Winning
Technology
Global Domain
Expertise
Customer-Centric
Approach
Comprehensive
End-to-End Platform
Customers Success Stories
We have demonstrated numerous success stories using Cobwebs platform, from pinpointing threats to solving complicated investigations. The power of this technology is unrivaled, and we stand behind its application as the best we have ever used. "
Threat Intelligence Analyst
Real-Time Fusion Center
Just wanted to share another success story and say that if it wasn’t for Cobwebs, this case would have easily turned out differently. Your platform is what identified the subject. I can't say enough how grateful I am that you've allowed us keys to this bus."
Human Trafficking Investigator
Public Safety Department
We have found Cobwebs responsiveness
to our business needs and the rapid development of solutions exceptional.
It has helped us ensure that our safety and risk assessment expectations are met effectively."
Risk Assessment Officer
Information Analysis Unit
Learn How We Harness AI for a Safer World
At Cobwebs Technologies, we believe in using OSINT for good. Our solutions are used to protect people and communities. They identify victims of human trafficking, assist in natural disasters, and track illicit activities that threaten our environment. Our technology empowers organizations to make better-informed decisions, take proactive measures to mitigate risks, and ultimately contribute to a safer, more secure world for everyone.
An Award Winning Technology
Our innovative technologies and customer-centric solutions are recognized globally.
Read their reviews to learn what makes our technology stand out from the crowd.












Compliant and Certified
We place the utmost importance on information security and comply with the most rigorous security standards, global regulations and privacy protection laws to ensure safe and compliant workflows for our customers.
SOC2

GDPR

Privacy Policy

CyberRighTech
SOC2

GDPR

CyberRighTech

Privacy Policy
and Detect Threats